
Protecting your devices from cyber criminals is essential in today’s digital age. Cybercriminals are always innovating and evolving their techniques, so it’s important to stay one step ahead. In this article, we will discuss simple tips to help you protect your devices and keep your online accounts safe from the threat of malicious hackers.
1. Install and update antivirus software
In order to protect your devices from malicious cyber criminals and their intrusive techniques, it’s important to install and use antivirus software. This type of software provides an extra layer of security for your computer by scanning the data you come across on the internet and searching for malicious programs or viruses that could put your device at risk. Antivirus software works to detect and prevent unauthorized access, preventing malware from infecting your system.
It’s important to keep both antivirus software and its virus definition files up-to-date — these are regularly updated databases that tell the program how to recognize potentially dangerous files. Regularly updating gives your antivirus program an edge in protecting you against new viruses that may crop up, so be sure to set it up so that your system will automatically download and install these updates whenever they become available. It’s also a good idea to run diagnostics with a reliable antivirus scanner on a regular basis — this is especially true if you notice any unusual activity on your machine or notice anything out of the ordinary with its performance.
2. Enable two-factor authentication
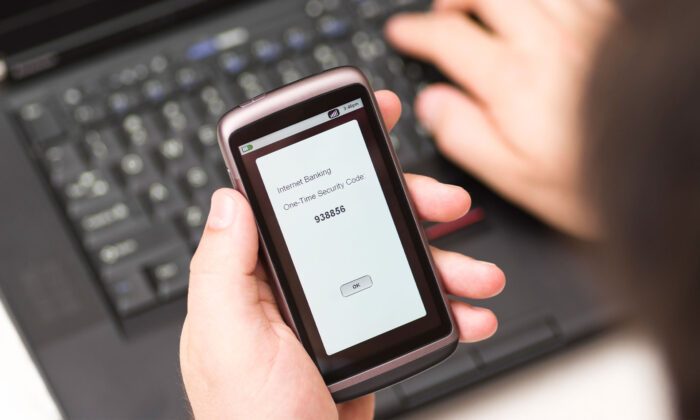
Enabling two-factor authentication (2FA) is one of the best ways to protect your data from unwanted access. 2FA works by requiring a second step after entering the password. It will ask for additional verification such as a PIN or biometric authentication before granting access to the account. This offers an extra layer of security to help prevent cyber criminals from accessing your sensitive information or infecting your devices with malware.
Another layer of security can be found in multi-factor authentication, which requires two separate forms of identification, such as a password and pin or fingerprint scan. This type of security goes one step further than 2FA and makes it even more difficult for hackers to compromise your device.
When using both types of authentication, make sure all authentication codes are unique, strong, and not shared with anyone else. Create unique passwords that use a combination of lowercase letters, uppercase letters, numbers, and symbols. Also, consider enabling account recovery options so that if you do lose access to your accounts due to a malicious attack or forgotten credentials you have ways to regain access without much difficulty.
3. Use a VPN
A Virtual Private Network (VPN) protects your data by encrypting it as it passes through the internet, adding an extra layer of security to any sensitive information you share online. A VPN also hides your IP address and makes it difficult for potential attackers to trace back to your device. You can use consumer-grade or enterprise-level VPNs depending on the level of security you require, and many devices have built-in VPN options that guarantee safe connections when logging into public WIFI networks. To further protect your online identity, be sure to use different credentials for each account wherever possible and adjust privacy settings to limit access only to certain people or groups if needed.
Additionally, there are online resources to protect your data like https://policy.zte.com.cn/.
4. Use a strong password for all accounts

Creating and managing a secure password for all accounts requires attention to several details such as length, complexity, and frequency of changes. It is recommended that passwords be at least 8 characters in length with a combination of upper and lower case letters, numbers, and special characters.
To best protect user accounts from unauthorized use organizations should ensure they have policies and procedures in place designed to detect malicious attempts such as brute-force attacks or attempts using commonly used passwords. Taking proactive steps such as enforcing two-factor authentication solutions like biometric scanners may also be beneficial in protecting your system from data breaches.
5. Disable remote access
By default, most home and business networks are set to allow remote access for service technicians or system administrators. Unfortunately, this is a gateway for cybercriminals. It’s important to take the time to disable remote access if it is not necessary. Disabling this will prevent hackers from connecting and accessing confidential data from outside of your network. You can disable remote access by changing the settings on your router or firewall.
6. Use a secure cloud storage

Ensuring the security of your data in the cloud necessitates a comprehensive approach to cloud security governance. Using a secure cloud storage system is an initial yet crucial step in safeguarding your data from cybercriminals. While most cloud storage solutions provide essential encryption and other security measures, opting for providers that offer enhanced security features, such as multi-factor authentication (MFA), is imperative. MFA adds a layer of protection, necessitating two or more credentials for account access, thereby preventing unauthorized individuals from accessing sensitive data files and folders.
Leveraging a secure cloud storage service also enables the safe and efficient storage of substantial data volumes across multiple systems. Solutions range from encrypted boxes, which are cost-effective and straightforward to deploy, to zero-trust networks that, while pricier, provide superior control and security over data access and modifications across various devices. To fully realize these benefits, organizations must implement robust cloud security governance. This includes establishing and enforcing stringent policies and procedures for data access and sharing, as well as continuously monitoring for potential security vulnerabilities. Swiftly addressing any security incidents is vital to maintaining a secure and compliant cloud environment, ensuring the ongoing protection of sensitive information.
7. Don’t click on suspicious links
It’s important to be aware of any suspicious or unknown links that you may receive in emails from people that you don’t know. These links could be disguised as advertisements, offers, or requests. Even if they appear to come from someone you know, they may have been hijacked and are now sending out suspicious email links. When in doubt, it is best to delete the email without clicking on any of the attached files or embedded links.
By clicking on a link that has been sent by an unknown party, your computer could become compromised by malicious software including spyware, viruses, and other types of malware. Your computer could also be targeted for botnets and ransomware attacks with much worse consequences. It is therefore extremely important to be cautious with these message-borne threats and use caution when deciding to click on any suspicious or unknown link.
In conclusion, there are a number of steps you can take to protect yourself from cybercriminals. With the increasing prevalence of cybercrime, it’s essential that you take proactive measures to safeguard against this serious threat.
















